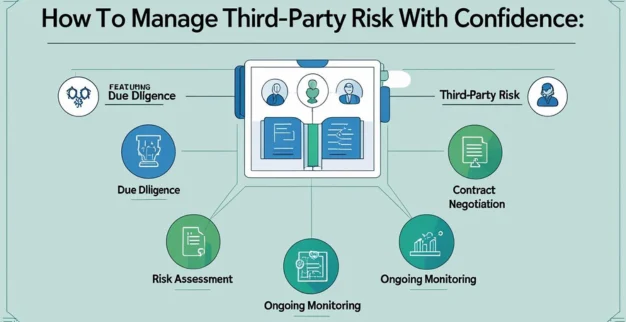
How to Manage Third‑Party Risk with Confidence
06 Aug 2025
Category: IT Security
In today’s interconnected world, third party risk management (TPRM) is more essential than ever. Trusting vendors and suppliers is integral to business operations—but that trust brings vendor risk to the table. When a partner falters, it can impact your data, your reputation, and your bottom line. Here’s how you can confidently manage third‑party risk and fortify supply chain resilience.
1. Build a Structured TPRM Framework
To manage risk effectively, start by building a structured TPRM framework. This includes:
- Cataloguing all third parties that interact with your data or systems.
- Classifying them based on criticality, data access, and business impact.
- Prioritizing vendors using a risk-based scoring model (“Likelihood × Impact”).
This framework ensures consistent, repeatable assessments and clear risk prioritization across your vendor ecosystem.
2. Conduct Thorough Due Diligence
Effective due diligence is the cornerstone of vendor risk control. When onboarding, ask vendors to complete robust questionnaires (like SIG) and support them with documentation—SOC 2, ISO 27001, audit reports, or compliance attestations.
Dive deeper by reviewing:
- Data access protocols and encryption standards
- Multi-factor authentication use
- Incident response plans and recovery capabilities
- Regulatory compliance and past auditor findings
With well-designed contracts, include audit rights, data privacy clauses, and clear remediation steps for breaches. This control layer reinforces vendor accountability.
3. Prioritize Vendors Based on Risk
Not every vendor bears the same level of risk. After cataloging vendors, rank them—high, medium, or low—based on data sensitivity, access level, and criticality to operations. This process helps focus resources on the most critical relationships.
For vendors with significant exposure—those handling sensitive data, infrastructure, or core services—expect deeper assessments and more frequent check‑ins.
4. Implement Continuous Monitoring
Static assessments are insufficient in a dynamic threat landscape. Move from one-time checks to continuous monitoring using technology, automated alerts, and open-source intelligence.
Modern tools and platforms can track:
- Security posture shifts
- Misconfigured assets (e.g. exposed cloud buckets)
- Emerging vulnerabilities or media buzz about a vendor
- Changes in ownership or subcontracting relationships
This real‑time visibility enables faster response and risk mitigation before minor slips escalate.
5. Leverage AI for Predictive Risk Insights
AI-powered TPRM platforms are transforming vendor risk programs. These tools can:
- Automate risk scoring
- Flag anomalies and changes in risk posture instantly
- Predict threats before they happen
- Streamline complex workflows and questionnaires
By embracing AI, you gain predictive insights, clearer dashboards, and proactive vendor risk controls.
6. Manage Fourth‑Party Dependencies
Vendor risk doesn't stop at third parties—many vendors depend on fourth parties. If those subcontractors are weak points, they can introduce unexpected vulnerabilities.
To address this, require transparency from vendors: who are their suppliers, what access do they have, and how are they secured? Reducing fourth‑party blind spots strengthens overall supply chain resilience.
7. Prepare for Incidents: Continuity & Response
A mature risk program includes incident response and continuity planning:
- Include critical vendors in your contingency planning
- Run joint cyber‑attack drills to practice coordination
- Identify redundancy or alternate providers to avoid single‑point failures
- Ensure your own environment has strict access controls and network segmentation to limit blast radius.
These preparations ensure that if a vendor falters, your operations stay resilient.
8. Cultivate a Risk‑Aware Culture
Risk management isn’t just about tools and processes—it’s also about culture:
- Formulate a cross‑departmental committee (IT, legal, procurement, compliance, business ops).
- Educate stakeholders on the importance of vendor security; include vendors in training and feedback loops.
- Regularly report metrics and vendor risk evaluations to leadership and boards, with visual dashboards and executive summaries.
By embedding vendor risk awareness into your organizational DNA, you foster accountability and shared ownership.
Why This Matters in 2025 and Beyond
Recent high-profile incidents—from global breaches via supplier penetration to the massive Marks & Spencer ransomware fallout—highlight the critical importance of proactive vendor risk management.
Regulatory frameworks like NIS2, DORA, and regional mandates are raising the bar for supply chain security, compliance, and vendor oversight. Organizations that can demonstrate structured, continuous TPRM programs will stay ahead of regulatory scrutiny.
Final Takeaway: Confidence Comes from Control
Managing third‑party risk with confidence means combining structure, technology, and culture into a unified TPRM strategy. Start with robust due diligence and vendor classification. Use continuous monitoring and predictive AI insights. Extend oversight to fourth parties. Prepare for incidents. And embed risk awareness into your organization.
By treating third‑party risk as an ongoing, collaborative program—not a one‑time checklist—you safeguard your people, data, operations, and reputation. In other words: confidence isn’t assumed—it’s engineered.